Our Managed Security & Reporting Services
QCM offers monthly Managed Security and Reporting Services to help small and medium-sized businesses with their IT Security and Compliance. Many SMB businesses do not have the available staff or the ability to continually manage and secure their IT infrastructure that protects their company and their customer’s valuable data. Few have policies in place to respond to a data breach. Left unprotected or ill-protected, a small business can be held liable for stored customer data affected by a breach.
Most standard cybersecurity companies offer standard protection such as Firewall, Anti-virus, Patching, and Spam Filtering that cover standard external threats, but in actuality, most security issues stem from internal threats.
Did You Know?
The involvement of the human element in breaches remained roughly the same as in 2024, hovering around 60%, the percentages of breaches where a third party was involved doubled, going from 15% to 30%.
(source: Verizon 2025 Data Breach Investigations Report)
The most common, high-impact cyber attacks on SMBs in 2025 include phishing, AI-driven social engineering, ransomware, and credential theft
(source: IBM's 2025 X-Force Threat Intelligence Index)
Looking for other Security and Compliance Options? Cyber skills development or Managed Services? Or how about CMMC Readiness and Assessment Services? We offer a variety of security services to help you.
EMAIL US info@qcmtech.com
USE OUR CONTACT FORM
CALL US - If your situation is urgent, please reach out to Tim Kinnerup for assistance
Timothy Kinnerup, Sr. Vice President, Sales & Operations
(602) 851-7941 Direct
Why Security Matters to Businesses Like Yours
Can You Afford these Numbers?
- Eighty-one (81) percent of small businesses reported suffering a security breach, a data breach or both in the past year. AI-powered attacks were identified as a root cause in more than 40 percent of cyber events, a pivot from internal risks to external, technologically advanced adversaries.
- Among breached small businesses, 62.5 percent reported a total financial impact—including lost revenue, remediation costs and fines—of more than $250,000 in 2025. Within that group, more than a third of all victims (36.7 percent) faced costs exceeding $500,000, an increase from 2024.
Source: Identity Theft Resource Center
How will Your Customers React?
- 27% of small businesses with no cybersecurity measures in place have had customer credit card information stolen
- 50% of small businesses take 24 hours or longer to recover from a cyberattack, which significantly impacts operations and customer trust
- 51% of Small Businesses Admit to Leaving Customer Data Unsecure Source: Must-Know Small Business Cybersecurity Statistics for 2025
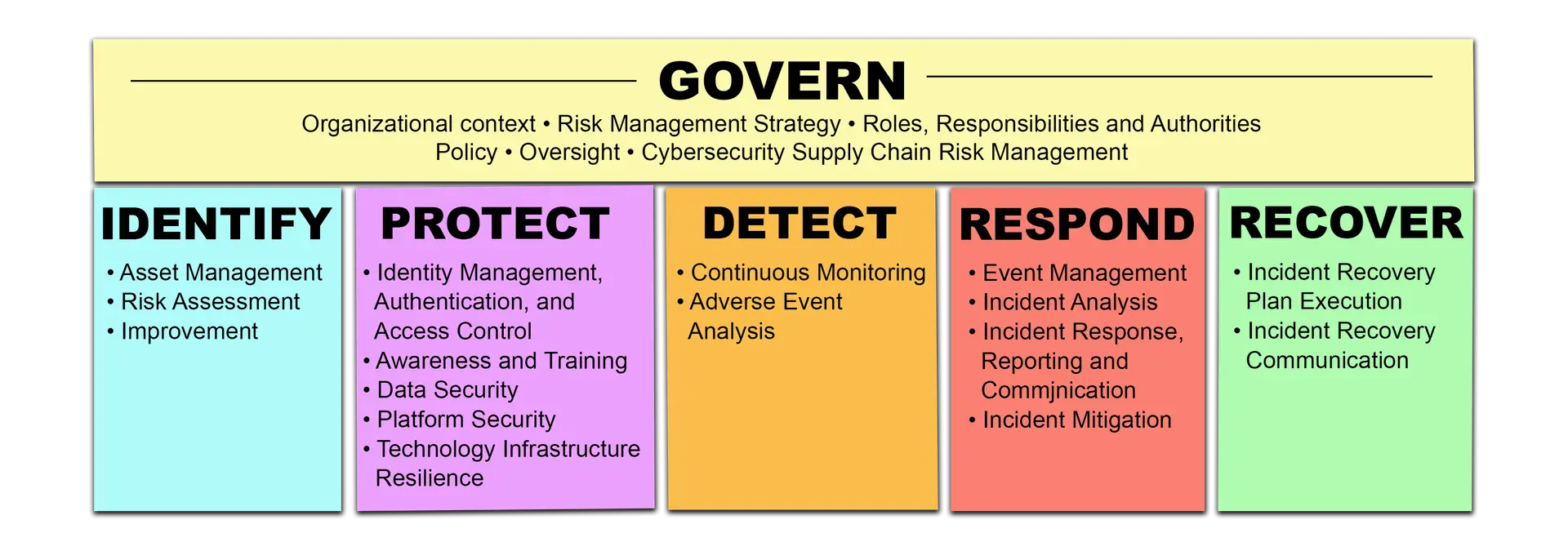
Recommended Best Practices by the NIST Cybersecurity [CSF] Framework
The Cybersecurity Framework
The core functions in the Cybersecurity Framework (CSF) — GOVERN, IDENTIFY, PROTECT, DETECT, RESPOND, and RECOVER — were selected by NIST because they represent the primary pillars for a successful and holistic cybersecurity program. They aid organizations in easily expressing their management of cybersecurity risk at a high level and enabling risk management decisions.
(Source: https://csrc.nist.gov/Projects/cybersecurity-framework/Filters#/csf/filters)
How Our Managed Security & Reporting Services Work
First, you’ll get to decide from our 3 levels of Security Reporting Services (Silver, Gold Platinum), which will determine your initial assessment and monthly services thereafter. Next, we’ll perform an assessment of your current security system at the level you decide upon. Our evaluation includes an external vulnerability scan, which addresses the major weaknesses faced by small businesses. After your assessment, we’ll show you the relative risks of what we discovered, and exactly what needs to be addressed. Next, we’ll use the NIST CSF measures to build and provide you with a recommended management plan that includes ongoing services to protect your business.
What You’ll Get with Your Managed Security & Reporting Services Plan
We enforce your IT Security Policies with regard to access control, computers, and network security. We also provide Security Alerting and continual scanning that looks for breaches behind your firewall:
- Automatically generated on a daily schedule
- Alerts sent to designated parties
- Alerts include built-in dynamic ‘action buttons’ for each threat, where you can instruct us to Remediate, Investigate, or Ignore
It Starts with Our Silver Plan, with 3 Plans to Serve Your Needs and Budget
We offer Silver, Gold, and Platinum Plans, with each covering additional internal security services. We are happy to provide you with more information on each respective plan.
We'll evaluate the following:
- Inbound Firewall configuration and search for known external vulnerabilities
- Outbound Firewall configuration
- The effectiveness of the current patch management
- Anti-virus and anti-spyware deployment
As well as:
- Administrator review
- Share permission review
- Physical security walkthrough
Value to Your Business
- More secure environment and peace of mind
- Reduced security management on your end
- Increased infrastructure reliability
- Avoid compliance fines and penalties
- Meets automation requirements for compliance frameworks
- Increase awareness of security-related issues
Now that you know how much our services can offer you at such fair pricing, reach out to us today and we’ll be happy to provide you with more information.
3 Ways to Reach Us
CALL US - If your situation is urgent, please reach out to Tim Kinnerup for assistance
Timothy Kinnerup, Sr. Vice President, Sales & Operations
(602) 851-7941 Direct
EMAIL US info@qcmtech.com
USE OUR CONTACT FORM
Additional Resources
Cybersecurity for Small Business - Federal Trade Commission
https://www.ftc.gov/business-guidance/small-businesses/cybersecurity
Framework for Improving Critical Infrastructure Cybersecurity and related news, information:
www.nist.gov/cyberframework
Additional cybersecurity resources:
http://csrc.nist.gov/
Most malware aimed at smaller businesses is focused on data theft, with password stealers, keyboard loggers, and other spyware accounting for nearly half of detected malware. The Sophos 2025 Threat Report covers these and other malware distribution mechanisms now in use, which range from phishing to malvertising and SEO poisoning. It also identifies the most common vulnerabilities attackers exploit and how the threat landscape is changing. It also states that ransomware remains the biggest threat, but old and misconfigured network devices are making it too easy for cyberthieves and hackers.
The report is based on the research and real-world experiences of Sophos’ threat, incident response and AI experts, and covers:
- The top cybersecurity challenges
- Latest social engineering tricks
- Dual-use tools
QCM Technologies
www.qcmtech.com
Scottsdale, Arizona • Est. 2001